What is a Virtual Private Network and Why You Should Be Using One
Posted 8 years ago
Virtual Private Networks
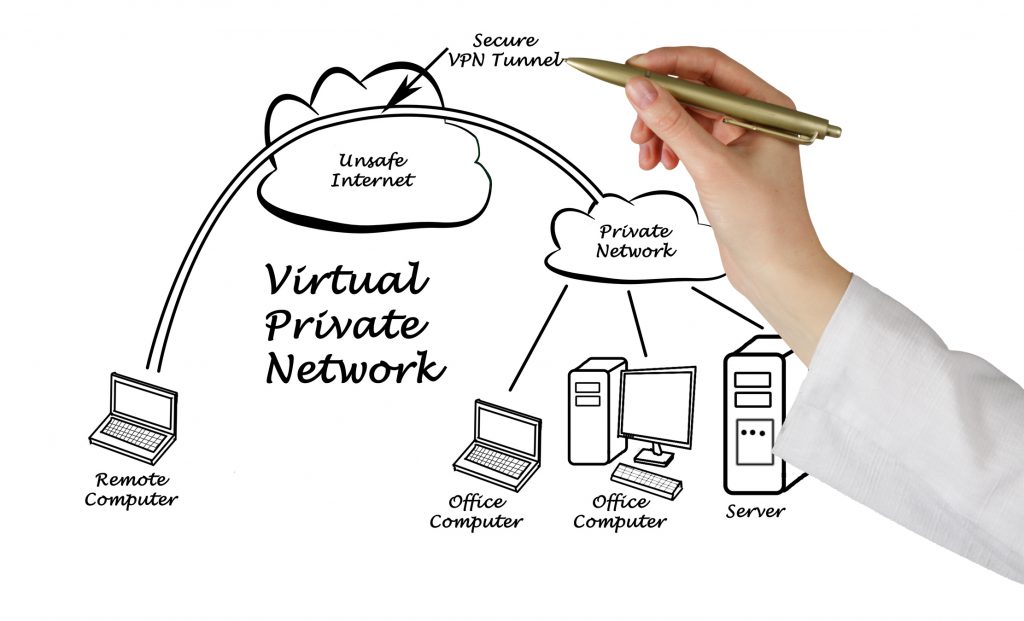
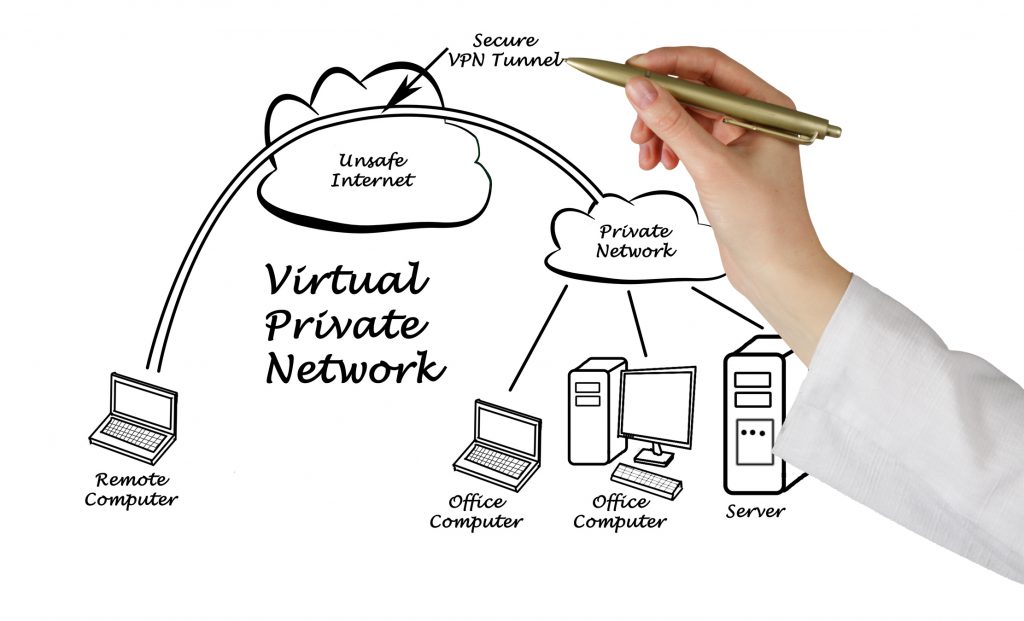
A virtual private network(VPN) extends a private network across a public network, allowing users to send and receive data across shared or public networks. It is typically a paid service with employs encryption to provide secure access over the internet.
Microsoft developed the first VPN in 1996 to grant employees access to the company’s internal network from home. Workers could access company files in their pajamas. More and more businesses began adopting them.
A VPN is the most secure way to connect to the internet without risking your online identity, privacy, and personal information. Any device that connects to the internet will benefit from the privacy VPN’s provide.
The Benefits of a VPN
- Replaces your IP address with an anonymous one – you can browse the internet in complete anonymity and masks your identity. A VPN also protects and secures your WiFi connection.
- Bypass government censorship – If you are in countries with internet restrictions and censorship, a VPN will route your traffic to a network in the United States.
- Encrypts your data – Connecting to a network through a VPN keeps all data secured.
- Improves streaming speeds – With their implementation, VPN’s increase Bandwidths and efficiency.
- Accesses blocked websites – Independent schools and libraries restrict access to certain websites or pages. A VPN will provide an encrypted connection to tunnel right through it.
- Accesses geo-blocked content while traveling – Geo-blocking is a method that companies and websites use to ensure their content and services are only accessible to people in the area they have their business or website. A VPN will allow you to access these geo-blocked websites in any geographical location.
How VPN’s Work
A VPN creates a secure tunnel between your computer and the various destinations you visit on the internet. You will be browsing from the geographical location of the server you are using, not from the site of your computer. By hiding your IP address and encrypting all your communication as it passes through the secure tunnel, you will be able to freely and anonymously surf the internet.
You should always connect to the web with your VPN turned on, so it will immediately connect your VPN provider’s router. Your information will be encrypted, jumbling up the text so that no one can read it.
Types of Encryption – Each With its Strengths and Weaknesses
Hashing is a one- way function that scrambles plain text which Hashing is a one-way function that scrambles plain text and is irreversible with decryption.
- Symmetric Cryptography or shared secret encryption. It is shared secret because the same key is used for the encryption and decryption. This method has been used for centuries. It uses a key to scramble data to make it unreadable. Someone on the other end needs the shared secret key to unlock the data. The key and results of the encryption can be changed.
- Asymmetric Cryptography is also known as public key encryption. This type of encryption has two keys; the public key encrypts the data and the private key decrypts the data. Anyone can use the public key to encrypt data. However, the private key can only be accessed by the intended recipient to decrypt the data.
Florida IT Pros
Your network’s security should always be a priority. There is a good chance that your network isn’t as secure as you think, but Florida IT Pros can help. Let us conduct a security assessment to determine where your security stands.
IT Services West Palm Beach
Florida IT Pros was founded in 2007 and has been growing ever since. After years of Fortune 500 experience as IT Engineers, Managers, and Directors we wanted to provide a higher level of service that many of our colleagues and we had experienced from other consultants or service providers. Call us at (561)206-2478 or Visit our website.
Florida IT Pros
1919 N Flagler Drive #300
West Palm Beach, FL 33407
561-206-2478
© Copyright 2018. All Rights Reserved.